For the ones who are not familiar with the term, BYOD stands for “bring your own devices”. Both the employee and the company can benefit from a properly enforced BYOD policy. Some studies have shown that it increases the productivity of an employee. But there are some who doubt the accuracy of these studies.
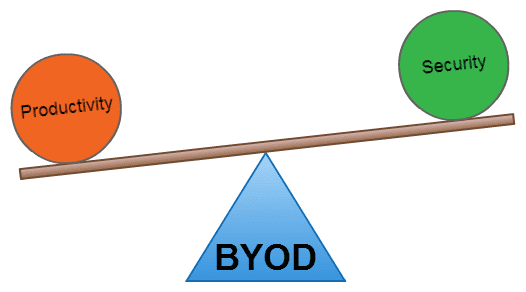
It could be a simple thing like replying to a mail before going to bed. Adding finishing touches to a presentation or something a bit challenging like delivering your final code. All these are extra hours work done by an employee on behalf of the company. So obviously there are benefits. The trick is to balance the benefits with the security risks.
Benefits of BYOD
Productivity is just one aspect, companies can save via many other ways too. For example the cost spent on buying and maintaining equipment is significantly reduced. For large companies there will be considerable saving on electricity. This will be very visible if you’re on an incremental unit charge plan.
Although there are many benefits, companies are reluctant to adopt a BYOD policy mainly because of security fears. Inability to track employees work becomes a distant second reason.
( diagram credit: Creately )
BYOD Security
Whether companies like it or not, employees do bring their own devices to the office. Very few companies ban employees outright from bringing devices. So it is logical to conclude that companies fear accidental security breaches rather than malicious acts by their employees.
In the beginning companies tried to secure the device by limiting the applications and the services available with the device. This approach was bound to fail from the beginning. Imagine an employee bringing their own device to work, installing all the necessary applications required for work and later finding out he can’t play “Cut The Rope” or use his favorite chat software in his personal time. Those are the situations that arose when companies tried to secure devices.
But fortunately there are ways to protect companies data without adding hundreds of restrictions to an employee’s device. Lets explore some of them:-
Application Management Software
Application management software, sometimes referred to as mobile management software, lets you manage applications instead of devices. So you can manage a company’s inventory management application while not touching “Angry Birds” or any other application that the employee has installed. You can encrypt the communication done via your applications, set access levels and in some cases delete those applications when a device is lost or an employee leaves the organization.
For organizations working with highly sensitive data there are custom made secure browsers and email solutions for that added protection.
Virtual Desktop Solutions
Another good way is to separate the company applications from the personal applications installed by employees. Users can access the company applications via the virtual desktop in a secure manner. The company can specify which device can access the virtual desktop, data encryption method and a whole lot of other things.
One drawback of this method is that you need to have a fast network connection to work smoothly. So in some cases this might not be the most reliable way to do office work. Also if the virtual desktop is going to consume lots of data then there might be a question of who’s going to pay the bill for data usage.
A somewhat similar variant of this is the virtual phone concept. Two virtual phones are created that use the same hardware. One for office work and one for personal use.
BYOD Has More Benefits than Risks
Overall a good BYOD policy can benefit both the company and the employee. However it is the responsibility of the organization to enforce the policy and to provide the proper infrastructure to make the process run as smooth as possible.
Do you work for a company that has a BYOD policy? Please share your thoughts and ideas in the comments section.
Did you like this article? Sign up for our RSS, join us on Facebook, on Twitter and on Google+ to get the latest Tweak Your Biz articles and updates.