Ransomware – malware that takes an individual’s computer hostage until a specific fee is paid – is a relatively new threat that has quickly become a significant problem. This particular kind of exploitation is particularly unnerving because it truly takes control of the victim’s computer, usually by restricting access to files and features.
There are a couple of known ways in which access might be restricted: the desktop might be locked, preventing the victim from launching Windows Explorer, or perhaps all of the user’s files will be encrypted. Regardless of the specific method used, the end result is the same.
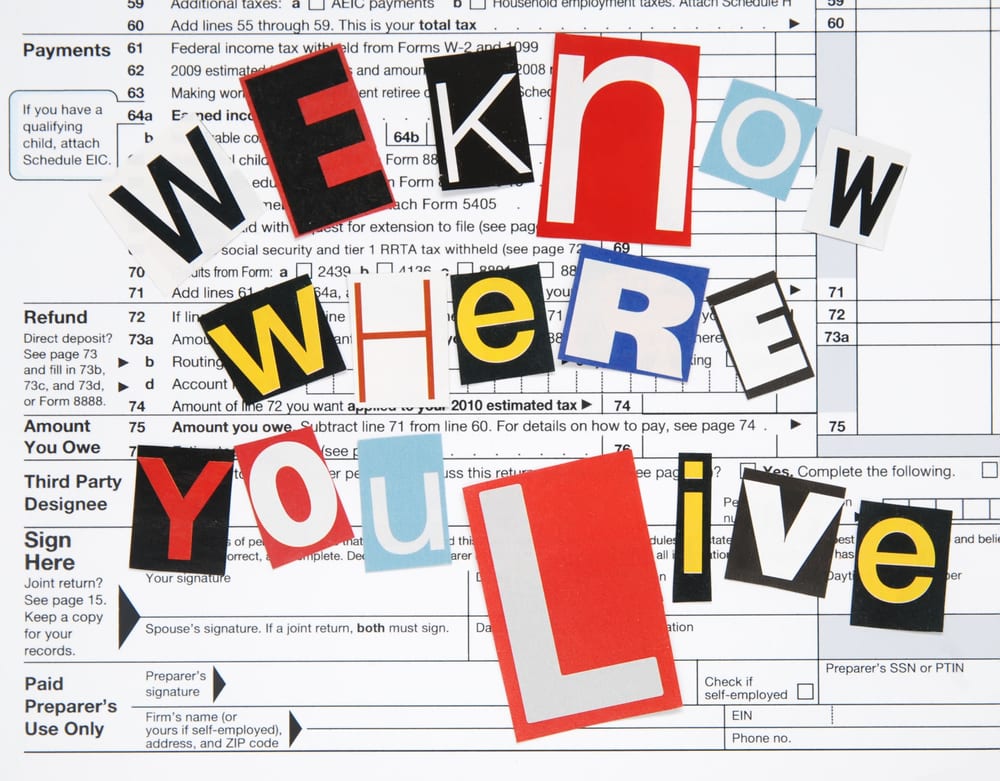
After restricting access to your files, ransomware will show a “ransom note”, usually meant to look as though it originates from the police, FBI, or related agency. This malware can also tell what country you’re in allowing the perpetrator to make the ransom note appear as though it is from your local law enforcement agency.
Aside from looking “official”, the ransom note will also give a reason for the “hostage” situation. Sometimes the claim is that the computer contains
How Does the Infection Happen?
Ransomware can end up on your computer in a variety of ways, and none of them mean that the victim has, in fact, been looking at illegal or pornographic content.
- If you have ever accidentally opened an email attachment from a spam email, for example, you could have easily infected yourself with ransomware. The malware might look like a normal document or presentation, but once the files are downloaded and opened, they could quickly infect your system. This goes for “normal” malware as well – don’t open attachments from strange or unexpected emails! The absolute best protection against threats is the use of computer virus protection.
- Using websites that have been infected by the criminals who perpetuate the malware is another way to infect your computer with ransomware. It’s important to note that the websites in question might not be obvious malicious websites. Some of the webpages responsible for infection are legitimate pages that have been “repurposed” by the people creating or distributing the ransomware.
- The bad guys also know that these days many people use tablets and smartphones to surf the internet and they have realized that there is a huge opportunity to make good money from it. Therefore ransomware for mobile devices, especially smartphones and tablets, is becoming more common. There are now plenty of security threats that can lock your tablet or smartphone, or even encrypt the important files stored on these devices.
- Ransomware is also being sent to your smartphones along with pornographic images. After getting these images, you will be unable to delete these images and the message will say it can make the images go away for a price.
Don’t Panic
The good news is that good computer security products can help stop malware before it infects your computer. The bad news is that perhaps because security software is becoming more adept at preventing malicious installations, ransomware is now being created for mobile devices.
If your mobile device – a phone or tablet, for example – becomes infected, do not pay the fee! Although the sight of the ransom note is scary, it’s not a legitimate message from a law enforcement agency, and you should keep in mind that such agencies will not take control of your device in this manner and instruct you to pay a fine online. Any such message is not true, and does not mean that you’re being investigated or in danger of legal action.
Tools are available to remove the threat
Rather than pay the fee and risk the criminals not releasing your device, there are tools available that can assist you in recovering your data and eliminating the infection. If you don’t want to attempt to remove the threat yourself, remember that you can always take the phone, tablet, or computer into a professional shop that offers assistance in virus and malware removal. The service probably won’t be free; however, the price is well spent as it will ensure that the threat is eradicated.
You can also try a popular and effective method for removing ransomware from your smartphone or tablet without any fee. If your smartphone or tablet gets infected, you should remove the battery and let it sit for 20 to 25 minutes. After that reinsert the battery and reboot your smartphone. If this process works correctly, you should immediately conduct a factory reset after calling the tech support of your service provider to guide you through it. If this infection still controls your smartphone, you can call tech support.
The best strategy for Android users is to only download apps from the Google Play store and not from any other sources.
Avoiding this malware on a personal computer is more difficult as there are plenty of methods through which this infection may occur. As a thumb rule, computer users should be highly selective of anything that they download to their personal computers. Further, always make sure that seemingly legitimate updates, such as flash player, are originating from the websites with a security certificate, which is identified by a lock symbol in the left of the URL field of browser.
Protect Your Information
Take action to help protect your devices from ransomware. If you’re using your computer, ensure that you have security software that protects against malware as well as adware and viruses. Keep your operating system and programs updated in order to prevent infection through known security holes, and make sure that you routinely back up your files. This way if the computer does become infected, you can always restore the files once the threat is removed. Always make sure to keep computer virus protection software on all of your devices.
If you’re using a mobile device, stick to using apps that come from known, legitimate sources. Just like on your computer, you should consider regularly backing up all of the items on your mobile device and look into what security options are available to you.
Images: “threat to taxpayer from government /Shutterstock.com“
______________________________________________________________________________
Tweak Your Biz is a thought leader global publication and online business community. Today, it is part of the Small Biz Trends stable of websites and receives over 300,000 unique views per month. Would you like to write for us?
An outstanding title can increase tweets, Facebook Likes, and visitor traffic by 50% or more. Generate great titles for your articles and blog posts with the Tweak Your Biz Title Generator.